Most SaaS founders know their product is valuable. Fewer know how to protect the way it works before someone else copies the core idea. That problem gets bigger with multi-tenant SaaS. On the surface, multi-tenant design can look simple. One platform. Many customers. Shared systems. Separate data. But under the hood, the real value is often in how your product isolates tenant data, controls access, manages workload, routes requests, scales resources, applies policy, and keeps performance steady across many users at once. That is where a lot of the real invention lives.
Why Multi-Tenant SaaS Is Harder to Protect Than It Looks
At first glance, multi-tenant SaaS can seem like a normal software setup with a simple business twist. You build one product, many customers use it, and each customer sees only their own data and workflows.
From the outside, that sounds clean and easy to explain. But from a patent angle, that simplicity is exactly what makes this kind of system harder to protect than many founders expect.
The challenge is not that multi-tenant SaaS lacks invention. The challenge is that the most valuable parts of the invention often sit deep inside the system, hidden under words that sound generic.
Terms like tenant isolation, shared infrastructure, policy control, workload balancing, and role-based access can sound common even when the actual implementation is highly original.
If a business does not describe those deeper technical moves with care, the patent may end up covering only a broad idea while missing the true engine that makes the platform work.
The Outside Looks Familiar Even When the Inside Is Not
A lot of multi-tenant SaaS products look similar at the surface level. Many of them let different customers log into the same application.
Many store customer data in shared systems while trying to keep that data separate. Many promise scale, uptime, and security.
Because of that, founders sometimes assume their system is too common to deserve strong protection.
That is often the wrong conclusion. The real value usually comes from how the system solves hard tradeoffs that other teams have not solved in the same way.
One company may isolate data at the storage layer. Another may do it through request tagging and policy enforcement.
Another may divide resources based on tenant priority, workload type, or usage history. These are not just technical details.

These are the kinds of system choices that can become the heart of a defensible patent position when they are framed the right way.
Broad SaaS Language Can Hide Your Best Ideas
Many companies accidentally flatten their invention when they describe it. They say the platform supports multiple tenants. They say each tenant has separate access.
They say the platform scales based on demand. Those statements may be true, but they do not do enough work.
A strong patent strategy starts by asking a harder question. What exactly happens inside the system that makes those outcomes possible?
If your product routes requests through a tenant-aware processing layer before writing to a shared data service, that matters.
If your platform applies policy at the object level instead of only at the account level, that matters. If your scheduler shifts compute resources based on tenant behavior in real time, that matters.
For businesses, this means the drafting process cannot stop at product marketing language. A product page may say your platform is secure and scalable.
A patent needs to say how the architecture creates that security and scale in a way that is concrete enough to protect and broad enough to matter.
What Feels Like Standard Engineering May Still Be Patent Worthy
Founders often ignore their strongest ideas because the team sees them as obvious.
That happens a lot in deep technical products. Engineers solve a painful system problem, ship the fix, and then move on. Six months later, the solution feels normal because it is now part of the platform.
That is dangerous.
If your team had to make a hard design call to prevent tenant data leakage, reduce noisy-neighbor impact, preserve latency across shared resources, or enforce customer-specific control rules without spinning up separate environments, that design work may be exactly what deserves protection.
The fact that your team solved it does not make it ordinary. In many cases, it means you found a practical path through a technical problem that others still struggle with.
A smart business should train itself to spot these moments early. When engineering says, “We had to build our own layer for this,” that is often a signal worth capturing.
When product says, “No other vendor handles it this way,” that is another one. When customers praise something that appears invisible to them, such as consistency, isolation, or control, there may be patent value under that result.
Multi-Tenant Systems Solve Tradeoffs, Not Just Features
Multi-tenant architecture is not just a set of product features. It is a system of tradeoffs. That is one reason it is harder to protect than it looks.
You are often trying to get several things at once that naturally push against each other. You want tenant separation, but you also want shared infrastructure.
You want efficient resource use, but you also want predictable performance. You want fast deployment, but you also want customer-specific behavior. You want centralized control, but you also want local flexibility.
Those tradeoffs are where many patentable ideas live.
A business that wants stronger claims should stop thinking only in terms of features and start looking at tension points. Ask where the architecture had to balance competing needs.
Ask where the system had to make decisions in real time. Ask what part of the platform would break if your special logic disappeared. Often, that is where the invention becomes visible.
The Value Is Often in System Behavior Over Time
One common mistake is treating the invention like a static diagram. But multi-tenant SaaS is rarely static. It is dynamic. Tenants join, leave, scale up, change settings, trigger workflows, and create demand spikes.
Policies change. Usage patterns drift. Risk shifts across accounts. The system has to keep adjusting.
That means many of the strongest claim opportunities are not about the mere existence of components. They are about how those components behave over time.
A shared platform may detect a tenant-specific workload pattern and change processing rules before system strain appears. It may separate operations into classes and apply different resource paths based on the tenant profile.
It may move from a default rule set to a custom rule set when a trigger condition appears. It may watch for access conditions that create cross-tenant risk and automatically block the next step before exposure happens.
These moving parts matter because they show that the architecture is doing more than hosting multiple customers. It is actively managing a live environment with technical decision logic.
That kind of behavior can be much more valuable to claim than a simple statement that the platform is multi-tenant.
Common Terms Can Make New Systems Sound Old
Another reason this area is tricky is that the language around cloud software is crowded. Everyone uses the same few words. Shared services. Tenant isolation. Provisioning.
Policy engine. Access layer. Metadata control. Horizontal scale. Elastic compute. Once those terms appear in a draft, the invention can start to sound less unique than it really is.
This is not just a writing issue. It is a business issue. Weak framing can lead to weak protection. If the claim language sounds like a generic cloud stack, competitors may find easy ways around it.
Worse, the patent examiner may treat the invention like a routine setup rather than a specific technical solution.
The better path is to translate common software language into claim-ready architecture language. Instead of saying the system isolates tenants, explain how isolation is created, maintained, checked, and enforced.
Instead of saying the system allocates resources, explain the condition that triggers allocation, the input used to make the choice, and the effect on shared platform operation.
Instead of saying the system applies policy, explain when policy is selected, where it is applied, and how that affects downstream processing.
The Same Product Can Hide Many Different Inventions
Most founders look at the platform as one product. Patent strategy should look at it as a set of technical invention layers.
One layer may sit in data organization. Another may sit in workload control. Another may sit in user access. Another may sit in configuration inheritance across tenants.
Another may sit in exception handling for premium customers or regulated accounts. Another may sit in how analytics are generated from shared data without exposing tenant-specific information.
This matters for businesses because it changes how you prepare your filing strategy.
If you treat the whole platform as one broad concept, you may get one broad but weak story. If you break the architecture into invention layers, you may uncover several stronger paths for claim drafting.
That does not mean filing random patents on every small feature. It means seeing your platform with more precision.
The goal is to identify the parts that are hard to copy without rebuilding the system. Those are the parts that usually deserve the most attention.
Your Hardest Technical Problem Is Often the Best Patent Starting Point
A practical way to find protectable material is to ask a simple internal question: what was the hardest architecture problem we had to solve to make multi-tenant delivery work at scale for real customers?
That question tends to produce much better patent material than asking what features make the product cool.
Features are visible. Architecture decisions are durable. A shiny feature may change next quarter. A core system design often stays in place for years because so much else depends on it.
For example, a business may discover that its real invention is not the dashboard customers see. It may be the way the platform separates rule execution across tenant groups while still using a shared event backbone.
Or the way the system creates tenant-specific control spaces without duplicating service logic.
Or the way usage data is transformed before entering shared analytics so the model can learn system-wide patterns without exposing sensitive tenant context.
That is where claim drafting becomes strategic. It shifts from “What does the product do?” to “What technical move makes this business hard to replace?”
Competitors Can Copy the Outcome Without Copying the Exact Code
A common founder mistake is thinking a patent should protect source code. In practice, competitors rarely need your exact code. They need your core system logic and they need a way to get a similar result.
That is why multi-tenant SaaS patents need special care. The visible result may be easy to understand. The code is private. The protectable value sits in the architecture logic in between.
If your claims are too tied to implementation details that are easy to rewrite, they may be narrow.
If they are too high level, they may be weak. The goal is to capture the technical structure and decision flow at the right level so that a competitor cannot simply rebuild the same architecture under different labels.
For businesses, this means the drafting process should focus on repeatable technical patterns, not coding style. Capture how tenant context enters the system.
Capture where that context affects processing.

Capture how the system decides whether to isolate, share, escalate, split, throttle, cache, or reroute. Capture the architecture choices that another company would have to face if they wanted to recreate your product’s edge.
What Patent Claims Should Really Cover in a Shared SaaS System
A shared SaaS system can look simple from the outside, but the real value is rarely in the surface view.
Most of the time, the real edge lives in the hidden logic that lets many customers use one platform without breaking trust, speed, control, or performance.
That is why patent claims in this area need to cover more than the idea of shared software. They need to cover the system choices that make the shared model work in a useful and repeatable way.
Claims should cover the technical path, not just the business result
A lot of SaaS teams talk about outcomes. They say the system reduces cost, improves scale, or supports many customers at once.
That may be true, but patent claims need more than a business result. They need the technical path that gets there.
If your platform gives each tenant a separate experience while still using shared services, the claim should not stop at that outcome. It should reach the mechanism that creates the separate experience.

That may be a tenant-aware request flow, a rule engine that selects tenant-specific controls, or a data access model that changes behavior based on account context. The point is simple.
The claim has to reach the moving parts that produce the benefit, not just the benefit itself.
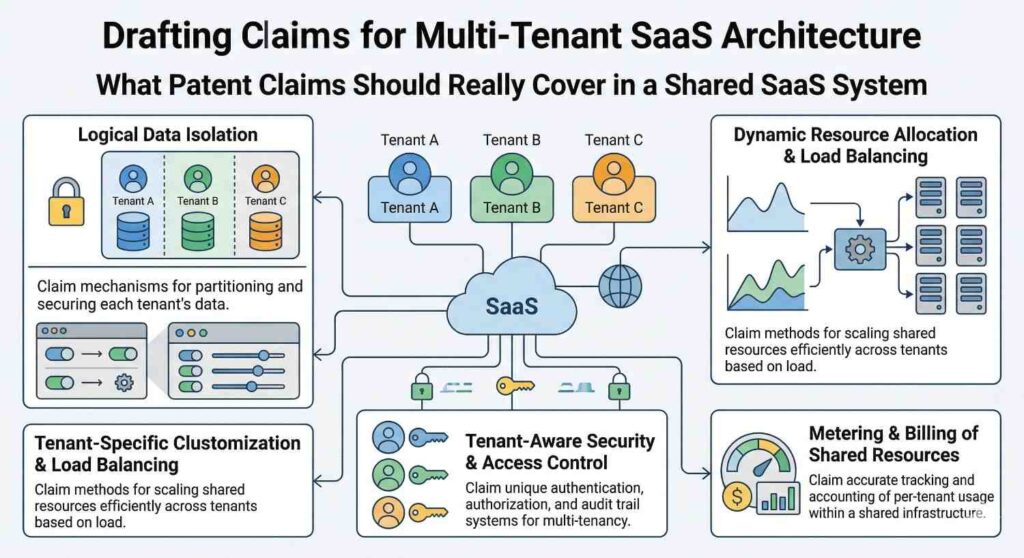
Claims should cover how tenant identity enters the system
In a shared SaaS platform, tenant identity is often one of the first things that shapes the rest of the workflow.
The system needs to know who the tenant is before it can apply the right controls, route the request, choose the right data scope, or enforce the correct policy.
That means one strong area for claims is the point where tenant context is introduced and how it travels through the platform.
If your system attaches tenant context to a request in a special way, uses it to drive downstream processing, or checks it at several layers before an action is completed, that is not just background detail. That may be part of the invention.
A useful way for businesses to think about this is to trace one customer request from start to finish. Watch where tenant identity first appears. Then watch where it affects later decisions. Those touchpoints often reveal claim-worthy structure.
Claims should cover separation logic, not just the idea of separation
Almost every multi-tenant SaaS company says it keeps customer data separate. That statement alone is not enough. Patent claims get stronger when they cover how the platform maintains separation under real operating conditions.
Data separation at rest
Data storage is one place where separation becomes real. Some systems use shared tables with tenant markers.
Others use partitioning rules. Others use tenant-linked objects that control access through an intermediate layer.
The claim should aim at the approach your architecture actually uses, especially if it solves a scaling or control problem in a new way.
Data separation during processing
Storage is only one part of the story. Data can also mix during processing, caching, analytics, logging, or workflow execution.
If your system keeps tenant data separate even while shared compute is being used, that technical choice may deserve just as much attention as storage design.
Data separation during output
The last mile matters too. Reports, dashboards, model outputs, exports, and alerts can all create risk if tenant boundaries are not enforced at the point of output.
If your system checks or rebuilds tenant scope before returning a result, that may be a valuable claim angle.
Claims should cover policy enforcement where it actually happens
Many SaaS systems talk about access control in broad terms, but real control usually happens at several layers. The system may check user role at login, tenant scope during query execution, feature rights during action selection, and exception rules during output generation.
A strong patent strategy should look closely at where policy is actually enforced. If the key invention is that policy is applied before shared processing starts, that matters. If the invention is that policy follows an object through multiple service layers, that matters too.
If the system selects one of several policy sets based on tenant state, usage class, or contract level, that may be even more important.
This is where many businesses leave value on the table. They say the system is secure, but they do not describe how the control logic is woven into the architecture.
The better move is to show where the system makes the control decision and how that decision changes the rest of the workflow.
Claims should cover resource control across tenants
A shared SaaS platform is not just about storing different customer data in one environment. It is also about managing shared resources across many customers without letting one tenant damage the experience for others.
That makes resource control a major claim area.
Handling uneven demand
Some tenants create heavy load while others use the system lightly. If your platform watches tenant-specific demand and changes resource use in response, that logic may be central to the invention.
The claim may need to cover how the system measures demand, how it classifies the tenant activity, and what it changes next.
Preventing noisy-neighbor problems
One of the hardest parts of shared systems is keeping one tenant from hurting the rest.
If your architecture detects harmful usage patterns and reroutes, delays, splits, or limits certain work before system quality drops, that is not just routine engineering. It may be one of the strongest parts of your moat.
Preserving service quality
Some systems guarantee different service behavior for different tenant groups.
That can include premium accounts, regulated users, or high-priority workloads. If your platform preserves service quality by applying tenant-aware scheduling or execution rules, that deserves careful claim coverage.
Claims should cover configuration logic, not just configurable features
Founders often focus on visible features when thinking about patent scope. But in shared SaaS, one of the hardest engineering challenges is often configuration.
The system needs to let many tenants behave differently without breaking the shared core.
That means the invention may sit in how configuration is stored, inherited, applied, updated, or overridden. If your platform lets tenants customize behavior through metadata rather than custom code, that may be important.
If the system merges global defaults with tenant-specific rules at runtime, that may matter even more. If tenant configuration affects which service path is used, that may be the heart of the claim.
From a business view, this is highly strategic. Configuration logic is often what lets a company scale revenue without scaling engineering work at the same rate. If that advantage comes from a special technical approach, it should not be treated like a side detail.
Claims should cover workflow decisions made in real time
Shared SaaS systems often do more than store and retrieve data. They make active decisions during live operation.
They select a processing route, choose a rule set, assign work to a resource pool, block actions that create cross-tenant risk, or change execution order based on system state.
These real-time decisions are often where the architecture becomes defensible.
Runtime selection of service paths
If tenant context affects which services are called or in what order, the claim may need to capture that decision flow. This is especially true if the routing logic improves speed, control, or isolation.
Dynamic rule selection
Some platforms apply different business rules or technical policies depending on who the tenant is, what they are doing, or what state the system is in. That kind of dynamic selection can be much more valuable than a static rule setup.
Automatic response to system conditions
If the platform notices strain, risk, or unusual behavior and changes its operation before failure happens, that response may deserve claim coverage too.
The stronger claims often describe not just the system pieces, but the trigger conditions that cause them to act.
Claims should cover shared analytics without exposing tenant data
Many modern SaaS products create value by learning across customers while still protecting each customer’s private information.
This is a rich area for claim drafting because it involves a hard balance. The platform wants system-wide insight, but it cannot expose tenant-specific data.
If your system transforms tenant data before shared analysis, builds aggregated models from controlled inputs, or limits what analytics outputs can reveal about any one tenant, that may be highly protectable.
A claim here should focus on the technical process that allows shared intelligence without breaking tenant boundaries.
For businesses, this area matters because it often drives both product value and customer trust. If you have found a useful way to do both at once, that is worth protecting with care.
Claims should cover the points that are hardest to design around
A helpful business test is to ask what a competitor would have to rebuild if they wanted to copy your edge without using your exact code. The answer usually points to the right claim territory.
If they would need to recreate your tenant-aware routing layer, that may be the focus. If they would need to copy your configuration model, your isolation checks, your policy flow, or your workload balancing logic, those are likely the areas that matter most.
This is one reason claims should not be written like product marketing. Product language explains what customers see.
Strong claims reach the system choices a rival would have to confront. That is where real defense starts.
Claims should leave room for growth
A good patent should protect what the system is today, but it should also leave room for where the platform is going next. Shared SaaS products change fast.
New tenant classes appear. Rules change. Services split. New layers are added.
That means the claims should not be trapped inside one narrow example unless that example is truly the core invention.
The better approach is to anchor the claim in the deeper system logic so it can still matter as the product evolves.
For founders, this is a very practical point. A patent filing should not only describe the current release.
It should cover the architecture pattern that will likely stay important as the business grows. That is how a patent keeps working after the roadmap moves.
The best claims connect technical detail to business defense
At the end of the day, patent claims for a shared SaaS system should cover the technical moves that protect the business itself.
They should reach the logic that keeps tenants separate, the controls that preserve trust, the scheduling that protects performance, the configuration model that enables scale, and the runtime decisions that make shared infrastructure feel reliable and safe.
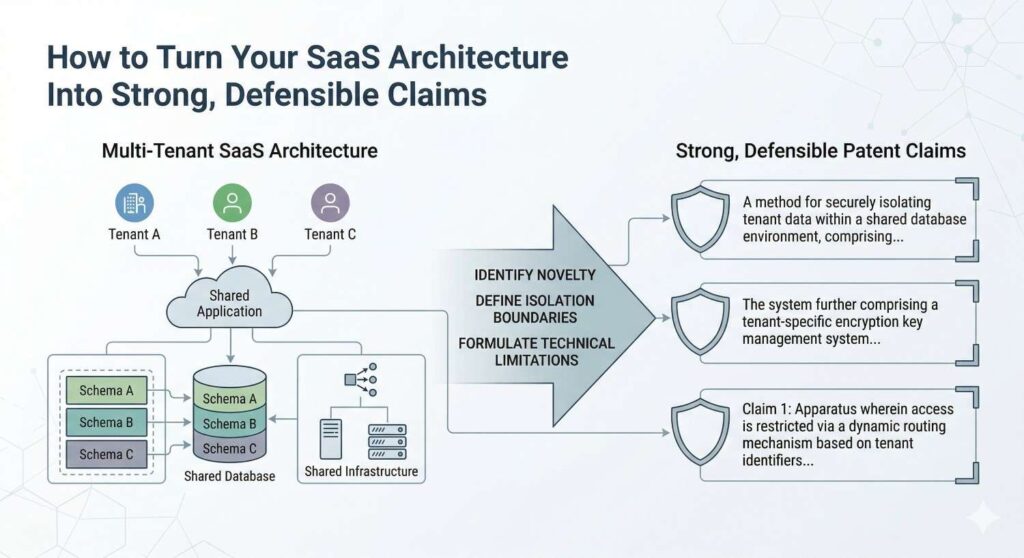
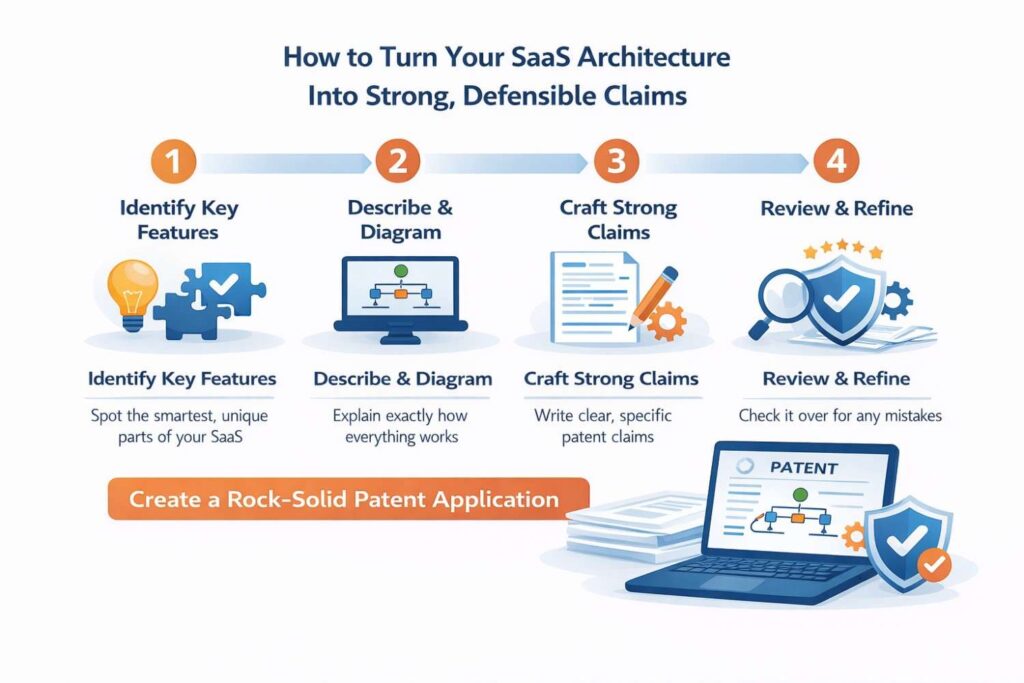
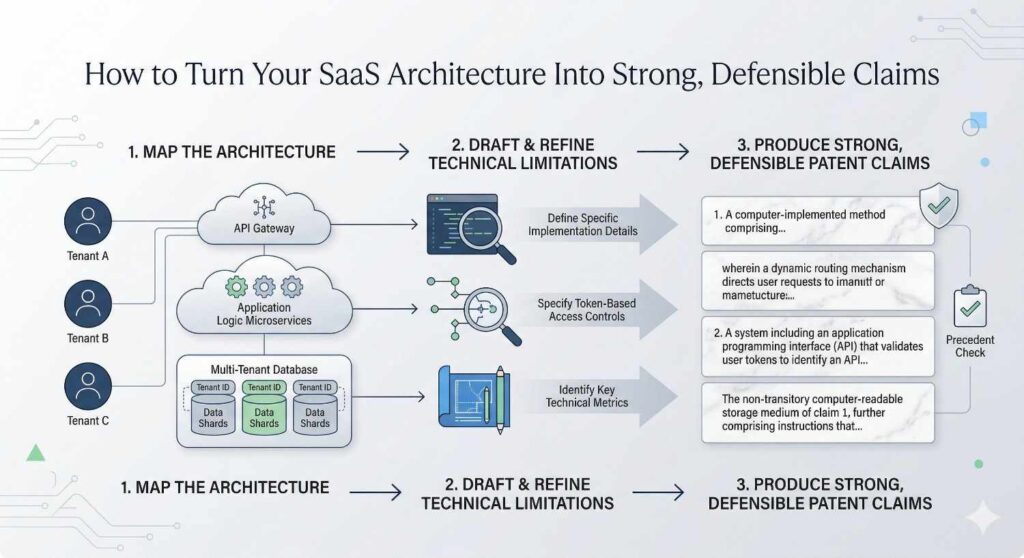
How to Turn Your SaaS Architecture Into Strong, Defensible Claims
A lot of founders know their product is hard to build. Fewer know how to explain that difficulty in a way that becomes real patent protection. That gap matters.
If your SaaS architecture solves serious technical problems, but your patent claims only describe the product at a surface level, you may end up with protection that looks fine on paper and does very little when it counts.
Turning architecture into claims is about translating deep system design into language that captures what makes your company hard to copy.
Start with the part of the system that would hurt the most to lose
The best claim work usually does not begin with the full platform diagram. It starts with the piece of the system that creates real leverage for the business.
That is often the layer your team depends on but customers never see. It may be the routing logic that keeps tenant requests clean.
It may be the policy engine that lets one shared system behave differently for different customers. It may be the way your platform manages isolation without forcing separate environments.

When you begin there, the claim process gets sharper. You stop trying to protect everything at once. You start protecting the part that actually gives the architecture its edge.
Find the hidden engine, not the shiny feature
Founders often describe the feature that customers buy. Patent claims usually get stronger when they focus on the hidden engine that makes that feature possible.
A dashboard is rarely the moat. The system logic underneath it often is.
If your customers love how fast the platform responds under heavy shared use, the invention may not be the response itself.
It may be the way the system classifies tenant traffic, directs it through different paths, and preserves service quality before strain spreads across the platform.
That is the kind of architecture move that deserves claim attention.
Ask what a copycat would need to rebuild
This is one of the most useful exercises a business can do. Imagine a smart competitor wants the same result your platform delivers, but cannot access your code.
What would they need to rebuild from scratch? The answer often points straight to the claim core.
They may need to recreate your tenant-aware data model. They may need to copy your way of applying customer-specific controls inside a shared processing flow.
They may need to mimic the logic that keeps one customer’s usage from dragging down everyone else. That is where the strongest claim material usually lives.
Turn product language into system language
A major step in drafting strong claims is learning how to move from product talk to architecture talk. Product talk explains outcomes. Architecture talk explains technical cause and effect. Claims need the second one.
Move from benefits to mechanisms
A sentence like “our platform securely supports many customers at once” may sound strong in a sales deck, but it does almost no work in a patent claim.
A stronger version explains what the system does to create that result. It may describe a request tagged with tenant context, evaluated against a tenant-linked rule set, and then routed to a shared service path that enforces storage and output limits tied to that context.
That shift matters because it gives the claim real structure. It shows a system doing something specific rather than simply aiming at a broad result.
Focus on technical verbs
One useful drafting habit is to pay attention to what your system actually does. It identifies. It selects. It routes. It partitions. It checks. It transforms. It limits. It reassigns. These actions help reveal the logic that can become claim language.
When your internal explanation is full of static nouns, the invention can sound flat.
When you describe the technical actions in the right sequence, the architecture begins to look like what it really is: a working machine with decision points that matter.
Follow one request through the system
A practical way to build defensible claims is to trace a single request from start to finish.
This works especially well in multi-tenant SaaS because so much of the invention appears during runtime rather than in a static system map.
Trace the first decision point
Start where the request enters the platform. Ask how the system knows which tenant is involved and what that changes immediately.
Does the tenant identity affect access, routing, policy selection, data scope, resource class, or workflow order? That first decision point is often more important than teams realize.
Track the changes downstream
Then follow the request deeper into the system. Watch how tenant context continues to shape what happens next. Does it control which storage path is used?
Does it change what processing is allowed? Does it determine whether data is transformed before analytics? Does it affect how results are filtered before output?
This step is powerful because it reveals the chain of technical consequences. Strong claims often come from that chain, not from one isolated component.
Look for repeated control points
If the same tenant-aware logic appears in several stages, that may be a sign that the real invention is not one feature but a broader control framework.
In that case, the claims may need to reach both the local steps and the larger architecture pattern tying them together.
Capture the tradeoff your architecture solves
Most valuable SaaS architecture exists because the team had to solve a hard tradeoff. Strong claims often become clearer when that tradeoff is named plainly.
Maybe you needed strict tenant isolation without giving up shared efficiency. Maybe you needed custom behavior for each customer without creating custom code branches for each one.
Maybe you needed platform-wide analytics without exposing tenant-specific data.
When you frame the invention around a solved tradeoff, the claim becomes more strategic.
It shows why the system exists in the form it does. It also helps separate your architecture from generic cloud setups that do not solve the same problem in the same way.
Write for design-around risk, not just filing speed
A weak claim can often be avoided with small changes in wording or implementation.
A stronger claim makes that much harder. This is why defensible claim drafting is not only about getting a patent allowed. It is about making sure the patent still matters after a competitor studies it.
Avoid getting trapped in one narrow example
If your claim is tied too tightly to one exact implementation, a rival may be able to shift one layer or rename one component and step around it.
The stronger move is to capture the deeper architecture logic while still grounding the claim in real technical detail.
That balance is not always easy, but it is where a lot of value is created. You want the claim to be specific enough to show invention and broad enough to cover close variations built for the same purpose.
Include fallback positions
A smart filing does not rely on one claim angle alone. It builds layers. One claim may focus on the main request flow. Another may focus on policy application.
Another may focus on resource control. Another may focus on output filtering or shared analytics. This creates more ways to protect the same core architecture from different directions.
This layered approach is one reason many fast-moving founders use PowerPatent.
It helps teams capture the real technical story in a way that is faster, clearer, and backed by real patent attorneys, so the patent does not miss the parts that matter most. You can see how it works here: https://powerpatent.com/how-it-works
Use your engineering history as claim fuel
Some of the best claim language comes from the choices your team already made. Design reviews, system change notes, scaling fixes, and internal architecture debates can all reveal why the final solution is special.
When a team remembers not just what it built, but why it rejected other paths, the patent gets stronger.
It shows that the final design was not random. It was a technical answer to a real system problem. That context helps shape claims that are both grounded and harder to attack.
The goal is not to describe the software. The goal is to protect the moat.
At the end of the day, turning SaaS architecture into strong claims means seeing your platform through a different lens. You are no longer just describing software.
You are identifying the technical decisions that keep your business ahead.
You are finding the architecture logic a competitor would struggle to avoid if they wanted the same outcome. You are turning invisible system design into visible legal protection.
Wrapping It Up
Drafting claims for multi-tenant SaaS architecture is not about using fancy patent language. It is about seeing your system clearly and protecting the parts that truly matter. That means looking past the surface. It means not stopping at words like cloud, scale, secure, or multi-tenant. Those words may describe your product, but they do not protect the deep technical choices that make your product hard to copy. The real value is usually in how tenant context moves through the platform, how shared resources are controlled, how policy is enforced, how data stays separate, and how the system keeps working well even when many customers are using it at once.